CAL Defense - Lifetime deal is out . Click Here
Welcome To Cyber Aeronautycs Ltd.
SECURING AIR & GROUND INFRASTRUCTURE
We are an aerospace and defense company in Bangladesh and engaged in research, design , development, manufacture, integration and sustainment of advanced technology systems, products and services.
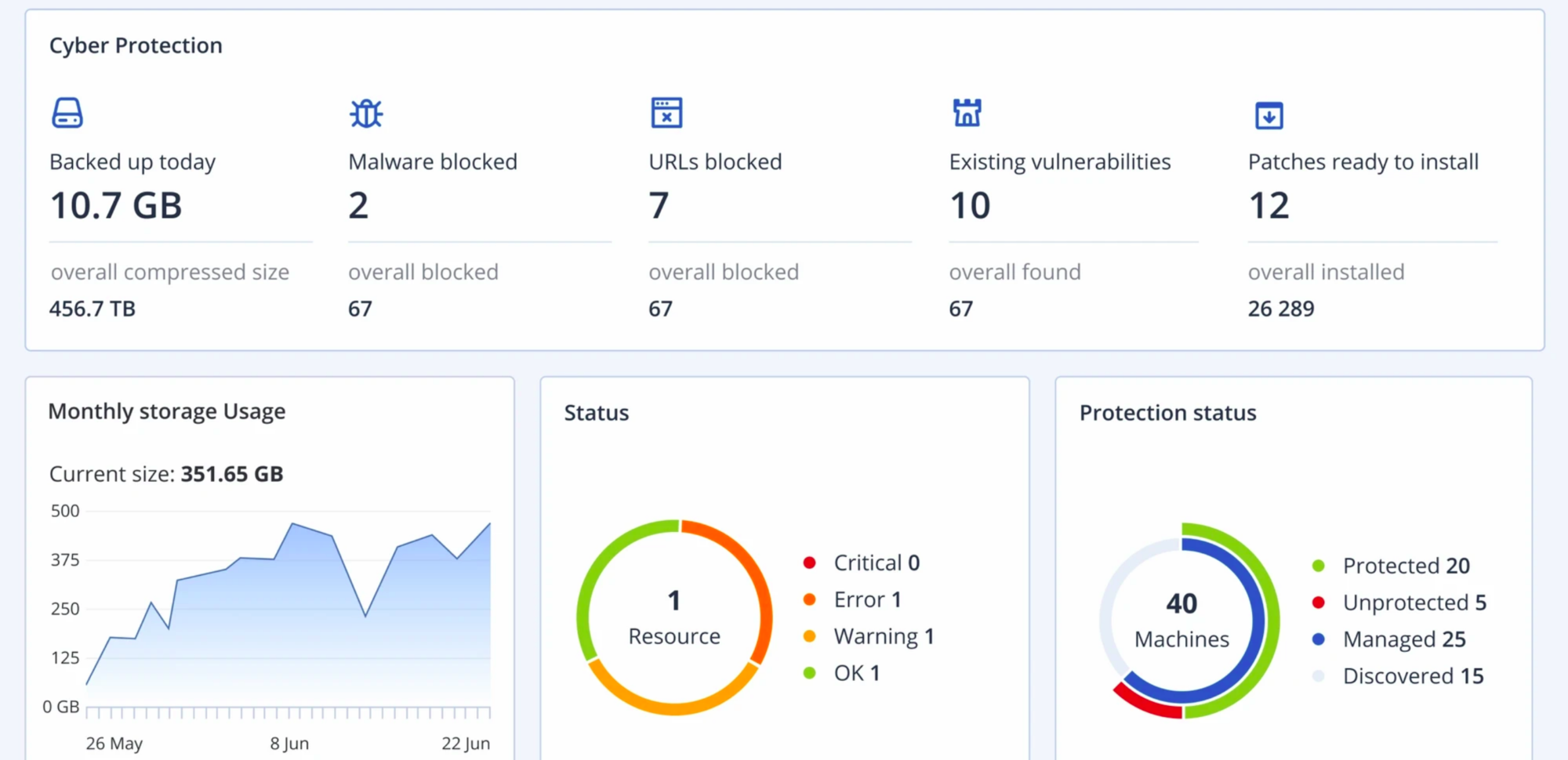
CAL Defense - Managed Device Protection & Management
Secure your business-critical data with next generation anti-malware protection
Cybercriminals strike at businesses every day in the hopes of extorting ransom payments or stealing sensitive information. "CAL Defense" use next-generation techniques to effectively halt both known and unknown types of malware in their tracks.

Key Features of "CAL Defense"
Vulnerability assessment
Keep your data safer by identifying and remediating vulnerabilities in your system. With our vulnerability assessments, you can scan your machines for vulnerabilities to ensure that all applications and operating systems are up-to-date and can’t be exploited by cybercriminals.
Protection for collaboration tools
Collaboration tools like WebEx and Zoom can help an organization become more efficient, but the problem is a lot of these tools are not secure. Proactively protect these collaboration tools with vulnerability assessments, patch management, code injection prevention and anti-malware capabilities.
Exploit Prevention
Until a patch is applied, your machines are vulnerable. With exploit prevention you can stop and prevent attacks from happening with memory protection, return-oriented programming protection, code injection protection and privilege escalation protection.
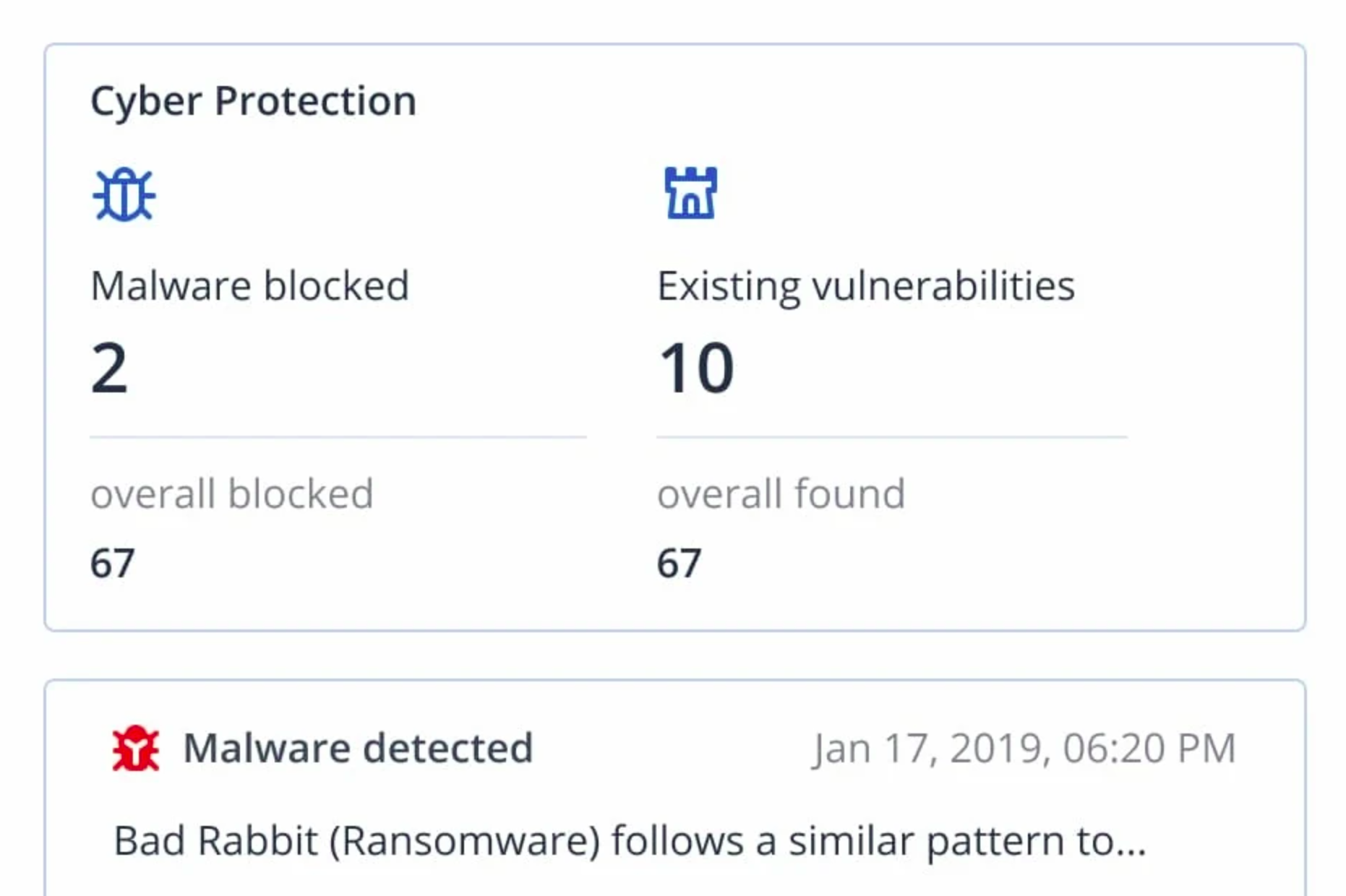
Anti-malware and antivirus
Actively protect your data, applications and systems from today’s advanced attacks. With CAL Defense, you gain extended functionalities of CAL Active Protection to protect your data in real-time with MI-based static and behavioral heuristic antivirus, anti-malware, anti-ransomware, and anti-cryptojacking technologies.
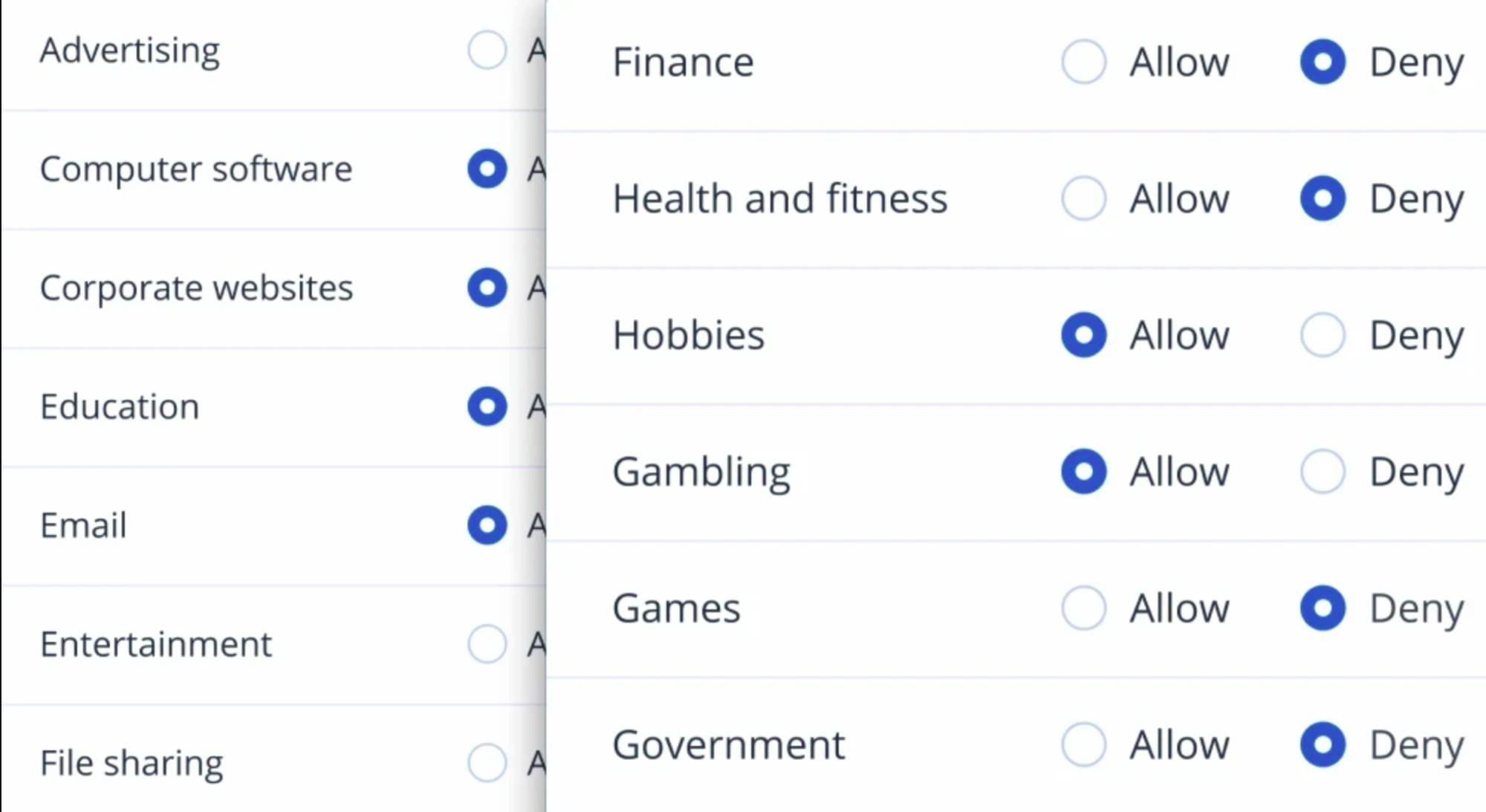
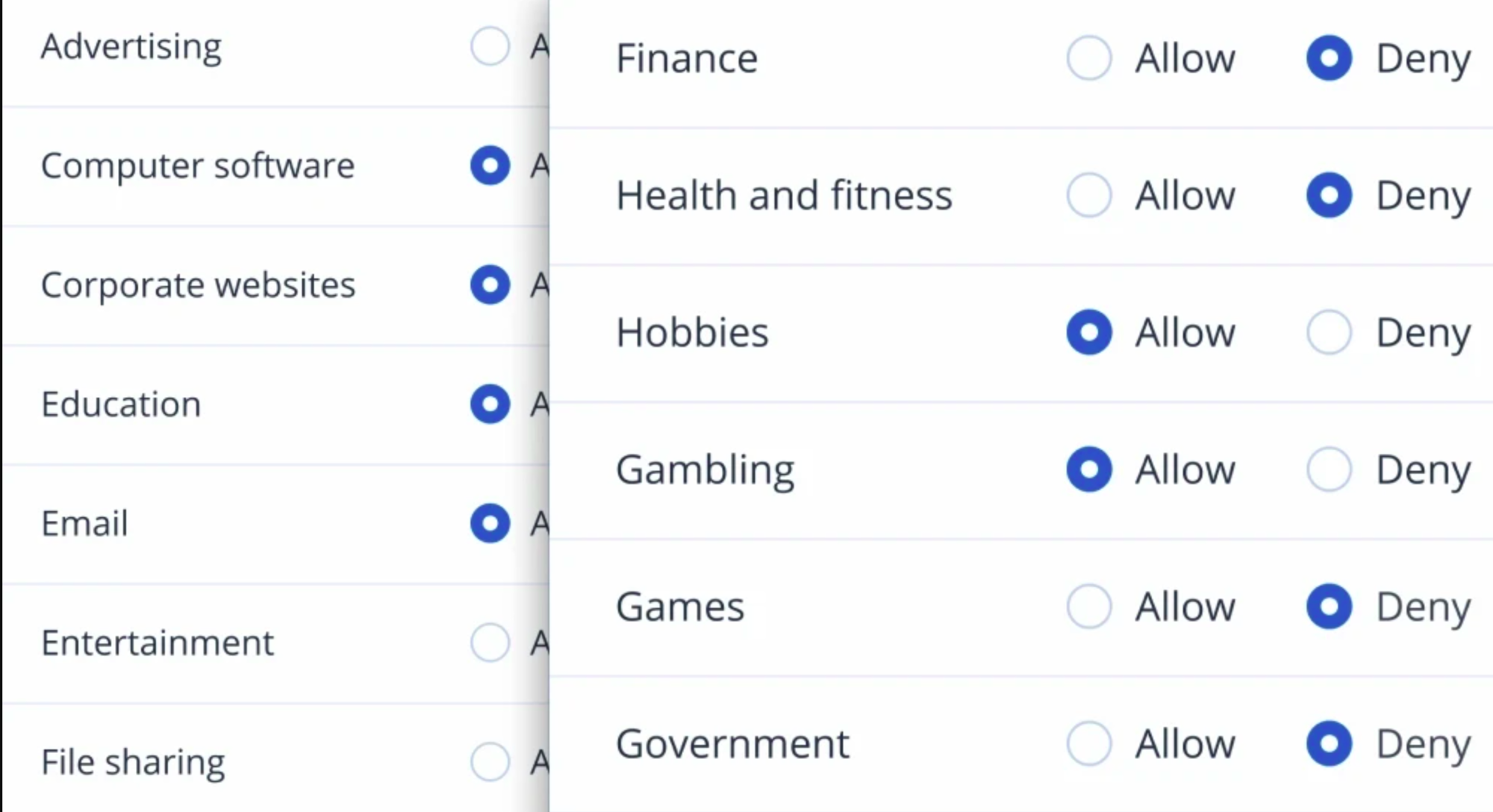
URL filtering and categorization
Achieve compliance and increase productivity by preventing attacks from malicious websites. With advanced URL filtering, you can control website access through a HTTP/HTTPS interceptor, deny and allowlists for URLs and payload analysis for malicious URLs.
Global Threat Monitoring & Smart Alerts
Our Cyber Protection Operation Centers (CPOC) continuously monitor the cybersecurity landscape and release alerts on potential threats of any kind. Receive real-time alerts on malware, vulnerabilities, natural disasters and other global events that may affect data protection, so you can prevent them.
Endpoint Protection Management
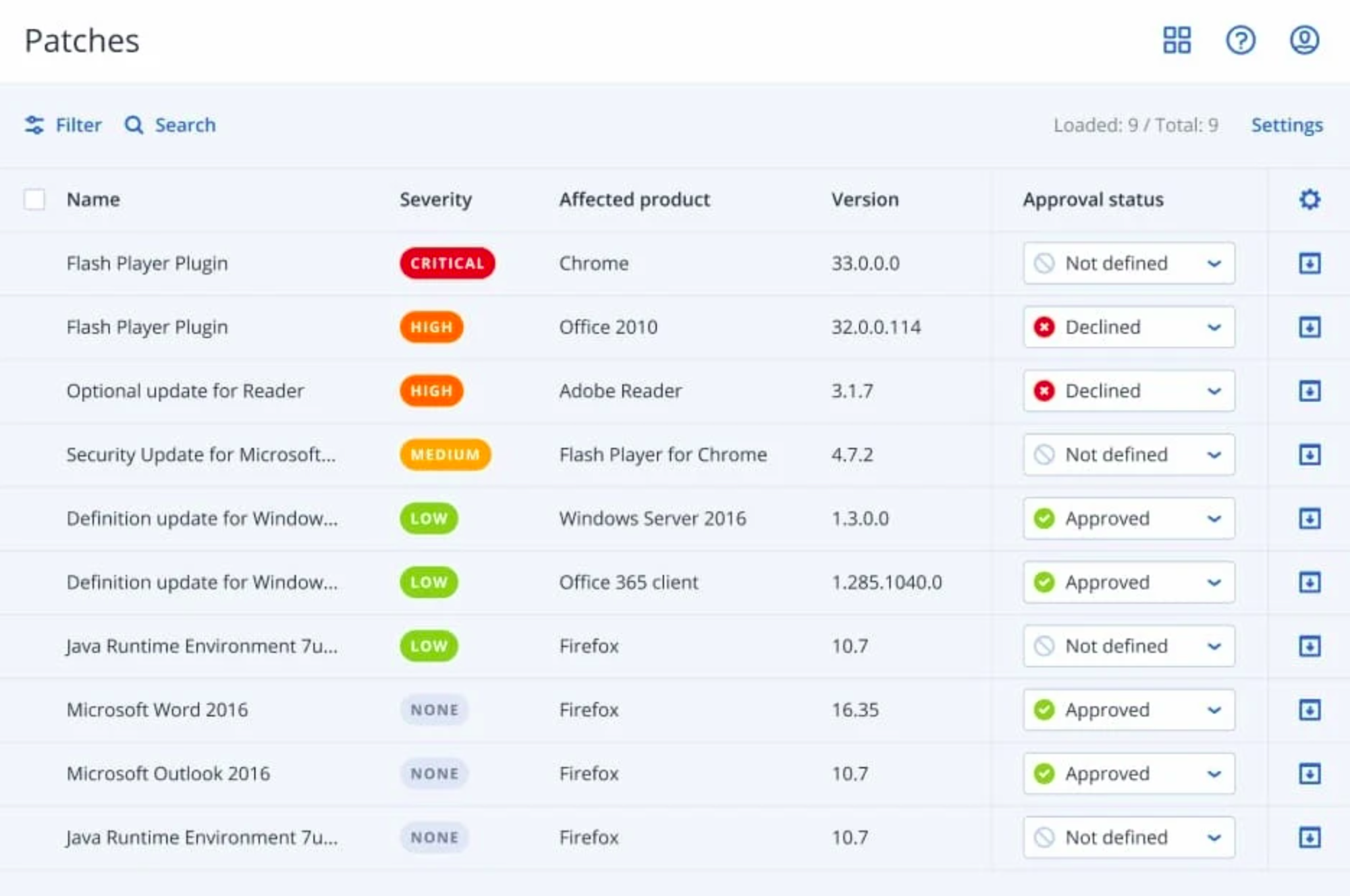
Patch management
Software patches and updates are essential to securing a business environment and can fix known vulnerabilities before they become issues. With patch management support for Microsoft and third-party software on Windows, you can easily schedule or manually deploy patches to keep data safe.
Fail-safe patching
A bad system patch can render a system unusable. Before a patch is implemented, an automatic image backup is performed so you can easily restore and rollback to a working state if there is an issue.
Windows Defender antivirus or Microsoft Security Essentials management
Eliminate complexity while ensuring that Windows Defender is properly configured. With CAL protection plans, you can control Windows Defender Antivirus and Microsoft Security Essentials detection events and enforce settings across multiple machines.
Auto discovery and remote agent installation
Simplify the process of installing multiple agents at once – in the cloud and on-premises. With network-based and Active Directory-based discovery you can remotely install and apply protection plans with ease – helping you keep your data safe.
Flexible Monitoring & Reporting
Simplified, at-a-glance reporting helps streamline your operations while giving you the insight you need to successfully protect your data. Customize your dashboard’s widgets to view reports on drive health, active alerts, missing updates and more – enabling you to quickly identify and remediate problems.
Remotely wipe devices
Keep business-critical data from falling into the wrong hands. You can now remotely wipe compromised or missing Windows devices. CAL Defense now makes it easy to prevent data from being deleted by disgruntled employees or being accessed from lost or stolen devices.
Remote desktop and assistance
Employees working from home may need access to files or apps on their work machines and they might not have a configured VPN. Share a secure link with end users so they can remotely access their machine.
100% Detection Rate
0% False Positives
100% High Performance
How to purchase ? Please contact us via chat or the contact form
Socials

Aerospace & Defense Company
Important
Our Industry
Government
National Security
Aerospace
Defense
Healthcare
Information Technology
Financial Services
Maritime
© Copyright 2022 . All Rights Reserved. Cyber Aeronautycs Ltd .
Registered in Bangladesh . Company Registration Number C-172611
