CAL Defense - Lifetime deal is out . Click Here
Welcome To Cyber Aeronautycs Ltd.
SECURING AIR & GROUND INFRASTRUCTURE
We are an aerospace and defense company in Bangladesh and engaged in research, design , development, manufacture, integration and sustainment of advanced technology systems, products and services.
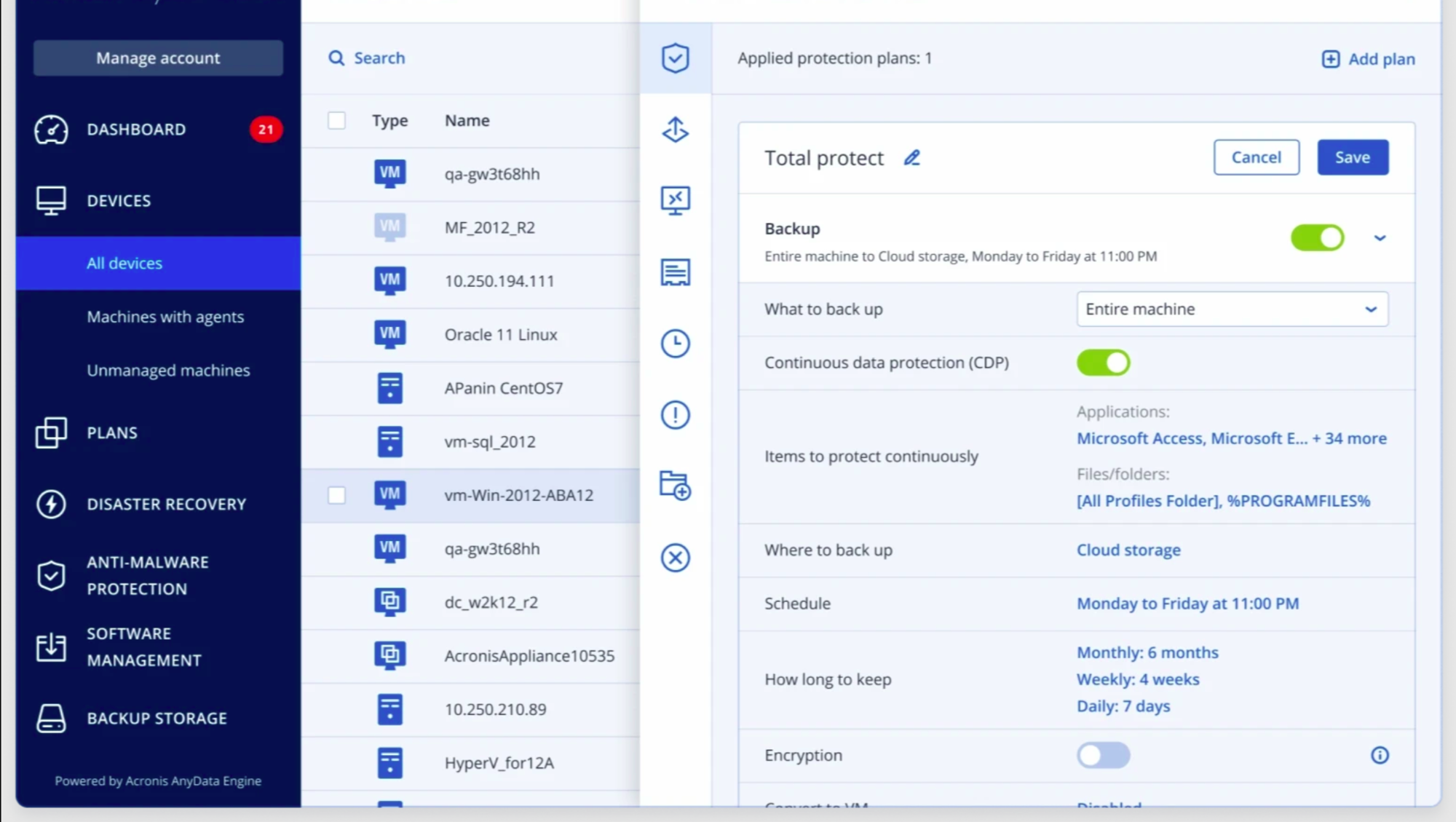
MSP Platform built to enable protection service
MSPs that offer services built on CAL Defense Cloud are more efficient and make more money, while lowering their clients’ cybersecurity risk.
Only an integrated cybersecurity and data protection solution enables you with
Next-gen Continuous Data Protection
Avoid even the smallest data loss in key applications.
Safe Endpoint Recovery
Integrate anti-malware updates and patches into the recovery process.
Data Protection Map
Monitor the protection status of files with classification, reporting and unstructured data analytics.
Smart Protection Plan
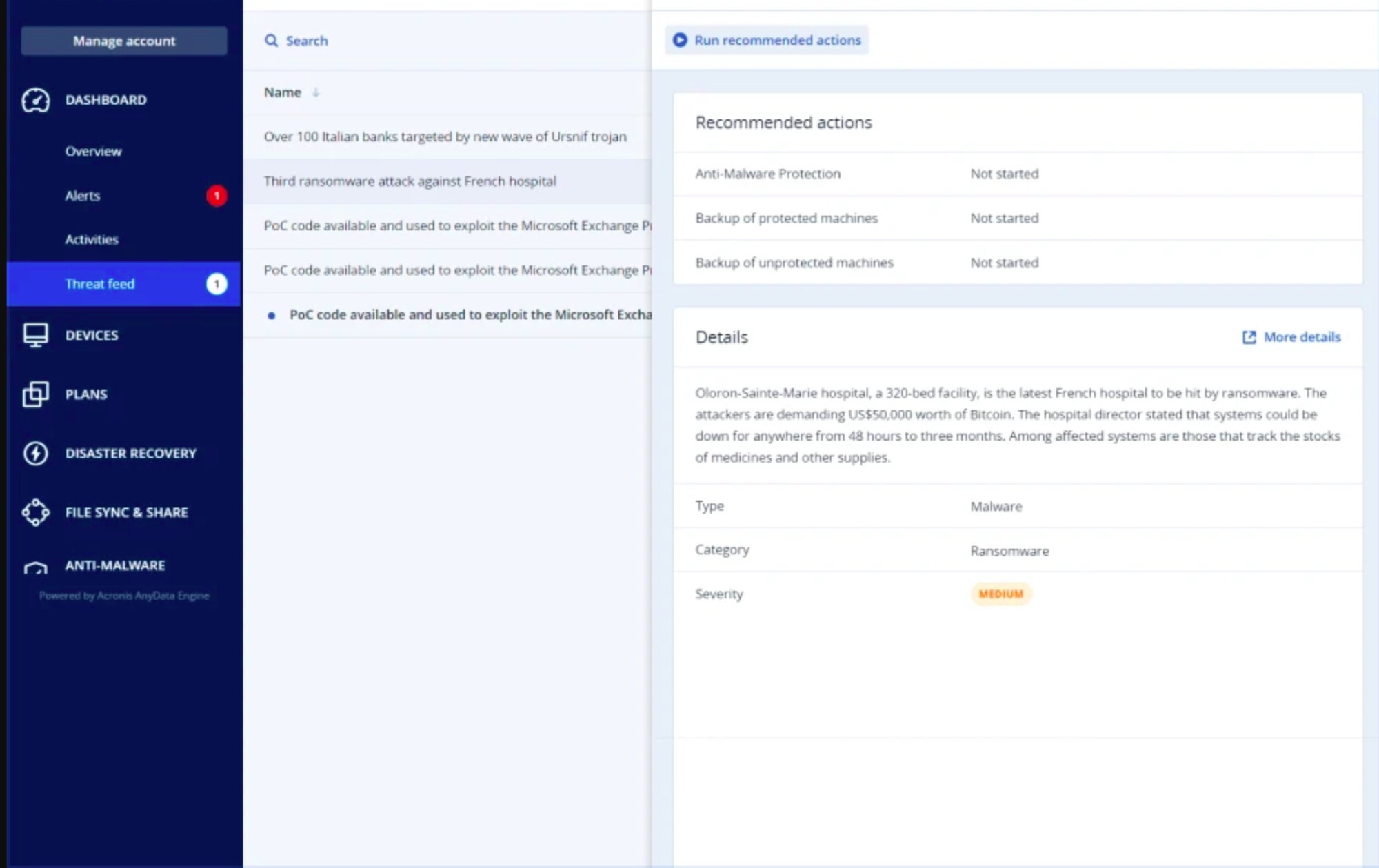
Auto-adjust patching, scanning and backup to current CPOC alarms.
Forensic Backup
Image-based backup with valuable, additional data added to backups.
Better Protection With Less Resources
Offload and enable more aggressive scans and vulnerability assessments in central storage, including cloud.
Fail-safe patching
Automatically backup endpoints before installing any patches to roll-back immediately.
Global & Local Allowlist
Create allowlists from backups support more aggressive heuristics by preventing false detections.
Create high-margin services to lower cyber risk
Superior cyber protection
Combining cybersecurity, data protection, and backup ensures better protection with fewer resources. Scan backups for malware to avoid reinfection, ensuring safe and malware-free recoveries. Avoid false positives with global and local allowlists. Simplify mitigation with easy forensics.
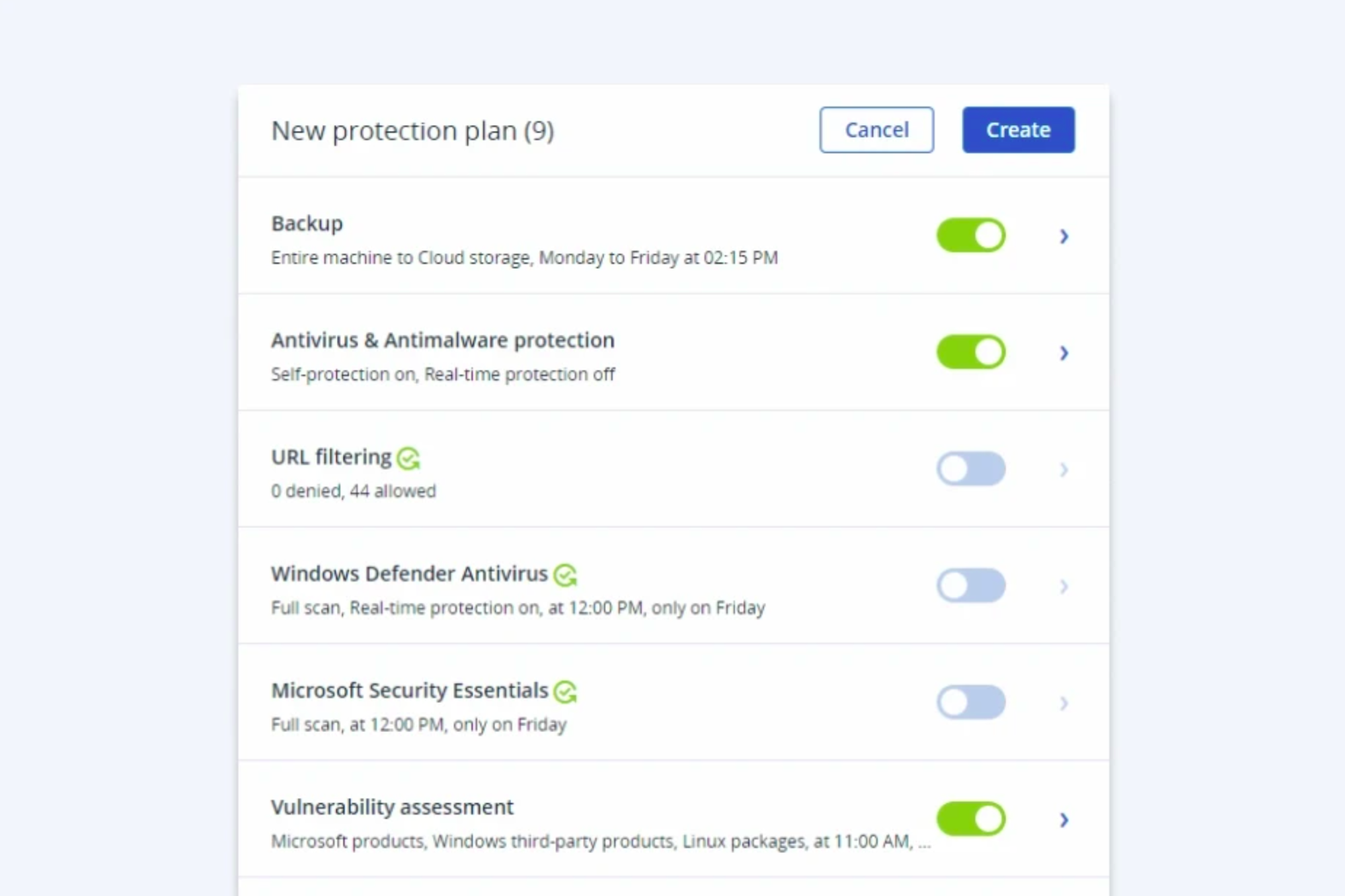
Customize by workload
With CAL Defense Cloud, you can easily attach the right protection to every workload at little to no cost. Additional advanced packs give you the flexibility to add robust protection for critical data, applications, and systems.
Streamline management
A single console enables you to set secure policies once and deploy them across multiple endpoints. Through a single interface, you can manage all of your clients and their usage without needing to bounce back and forth between cybersecurity and backup tools. It’s a simple interface to manage your clients’ infrastructure.

Integration is the difference
Using different solutions for data protection and cybersecurity creates complexity and broadens the threat vectors. Offering CAL Defense on the Acronis Cyber Cloud platform ensures the optimal protection for all data, applications, and systems.
Managed Server Backup
Your clients all have one thing in common, no matter their industry: data loss and downtime are catastrophic to their operations. As a service provider, the quality of the server backup and recovery services you offer matters. CAL enables you to deliver an integrated solution that combines the most secure server backup available with flip-of-a-switch disaster recovery — all through a single pane of glass.
Proactively Protect Client Data
To secure your clients’ business-critical data, simple backup isn’t enough. CAL enables you to deliver best-in-breed server backup that’s enhanced with cyber protection. A next-generation, AI-powered anti-malware engine scans backups as they’re created and as they’re retrieved to ensure data integrity. Even zero-day threats can be contained, thanks to behavioral detection that identifies and blocks suspicious processes.
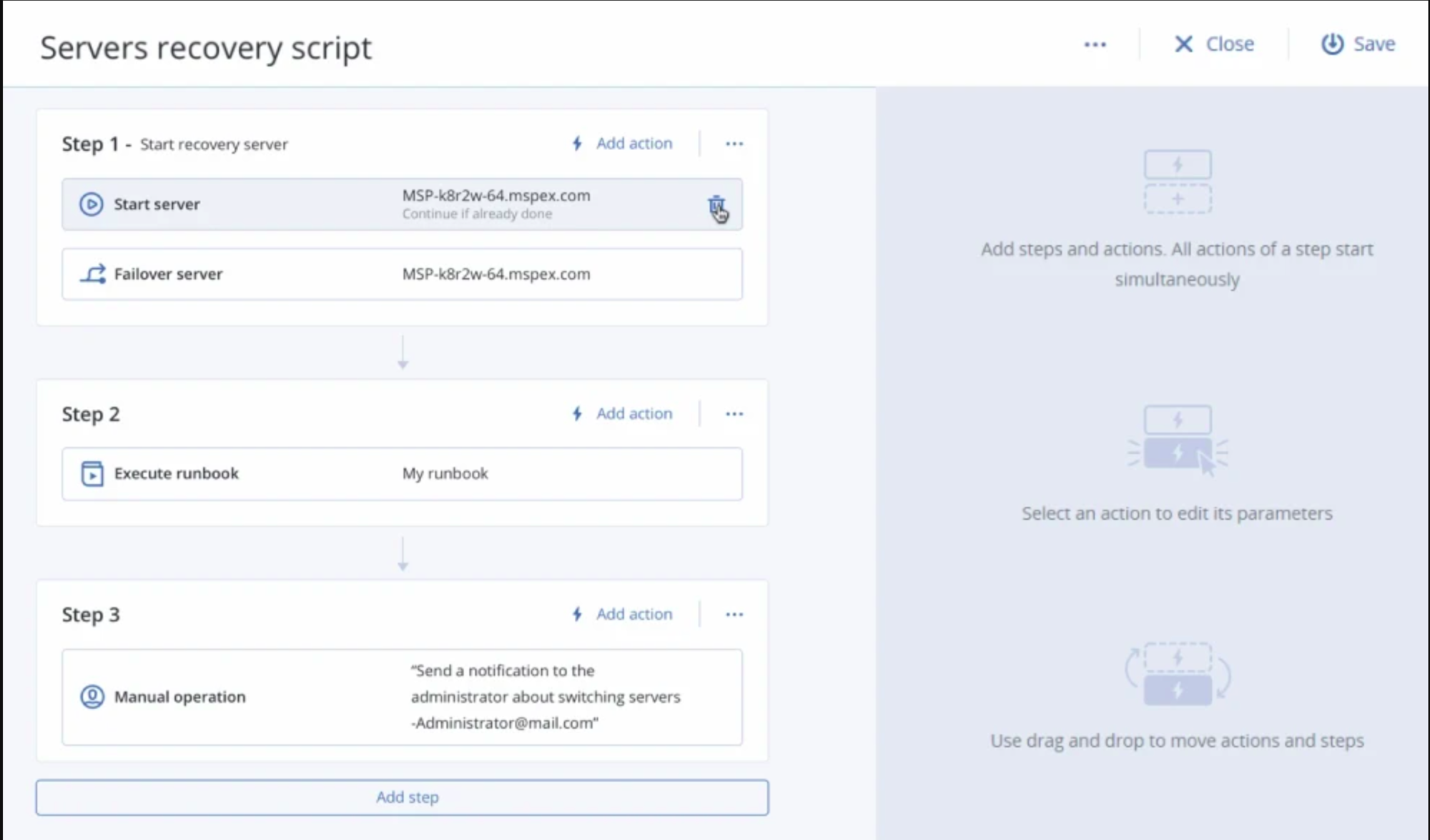
Enable flip-of-a-switch managed disaster recovery
Impress your clients with the ability to quickly fail over to the cloud when disaster strikes. CAL solutions enable you to slash RTOs by instantly spinning up entire systems in the cloud, and ultimately recovering to similar or dissimilar hardware. Providing disaster recovery doesn’t just increase your value offer — it deepens client relationships and increases retention.
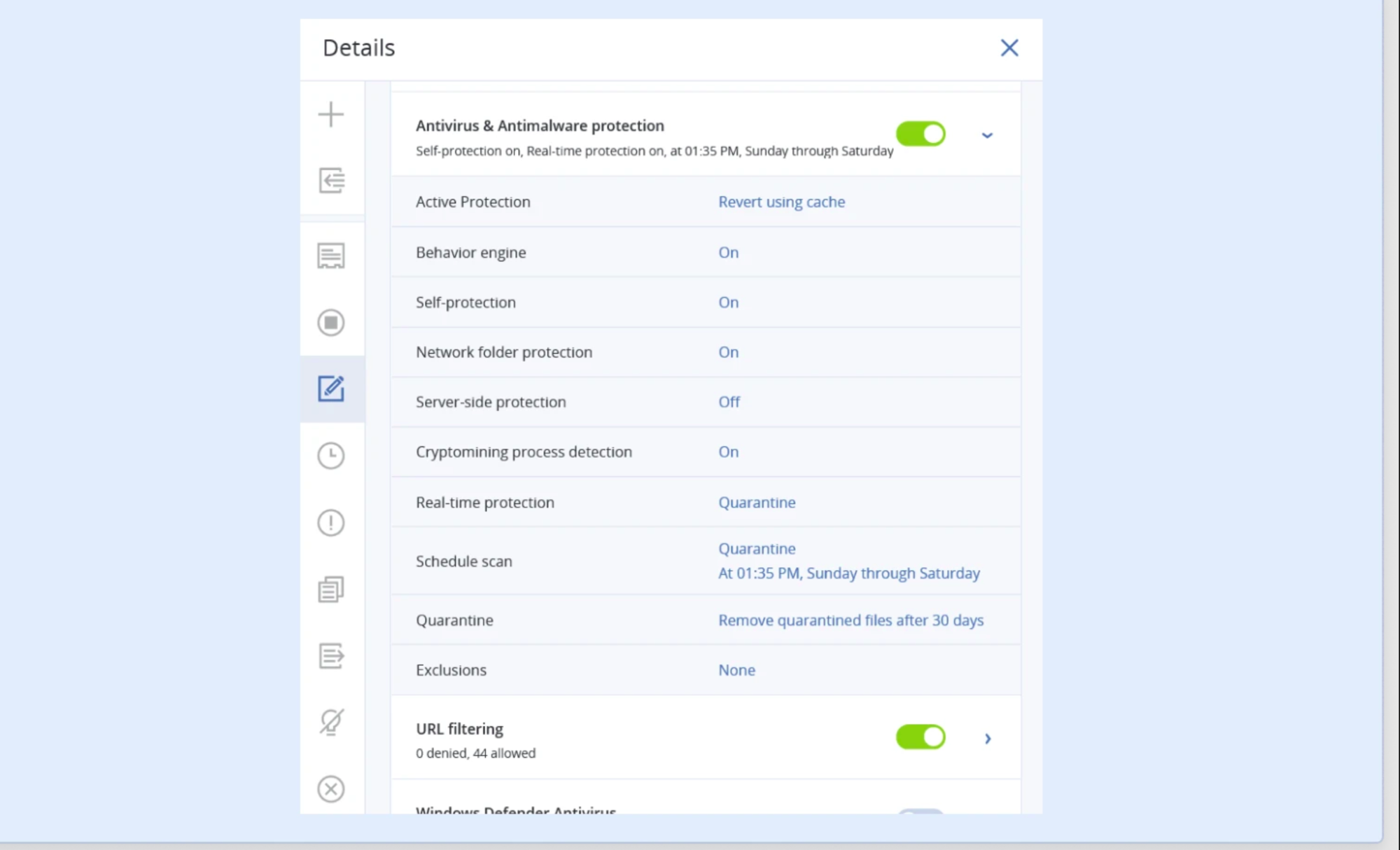
Ensure Comprehensive Cyber Protection
As businesses demand more from their IT services, MSPs are adopting more and more disparate tools that don’t work together smoothly, leaving clients exposed. CAL all-in-one solutions integrate anti-malware protection with data backup and endpoint protection management. This unique approach eliminates protection gaps and enables seamless remediation — no need to juggle multiple solutions.
Reduce Client Risk With A Comprehensive Security Approach
The risks of data loss, data leakage, and downtime can be prevented only with a security program that encompasses not just technology, but also people and processes. CAL empowers MSPs to improve their threat prevention services to provide proactive protection and resilient processes, while increasing end-users’ security-awareness.
Employ a proactive approach to threat prevention. Stop threats before they infiltrate a client’s endpoints
A successful attack on a client can leak or completely destroy their data or result in long costly downtime before you’re able to react. Be a step ahead of cyberthreats and reduce client exposure to them with an integrated approach to cyber protection.
“80% of breaches are new or unknown zero-day attacks”
Source: “The Third Annual Study on the State of Endpoint Security Risk”, Ponemon Institute, 2020
Leverage next-generation anti-malware technologies with built-in behavioral heuristics to stop malicious attacks, including ransomware, fileless attacks, exploitations, and zero-day malware, from infiltrating clients’ workloads, data, applications, systems.
- Next-generation anti-malware
- Effective against zero-day malware and fileless attacks
- Exploit prevention against known and unknown vulnerabilities
Stop online attacks with web filtering enhanced with machine intelligence
“50% of SMBs have experienced a web-based attack”
Source: “Global State of Cybersecurity in Small and Medium-Sized Businesses”, Ponemon Institute, 2019
Prevent threats from infiltrating clients by preventing access to known malicious websites or to legitimate domains that have been compromised. Proactive machine intelligence analyzes links in real time including extensive threat intelligence from CAL and our industry partners.
- Web filtering against malicious websites
- Prevention of drive-by-downloads
- Extensive threat intelligence
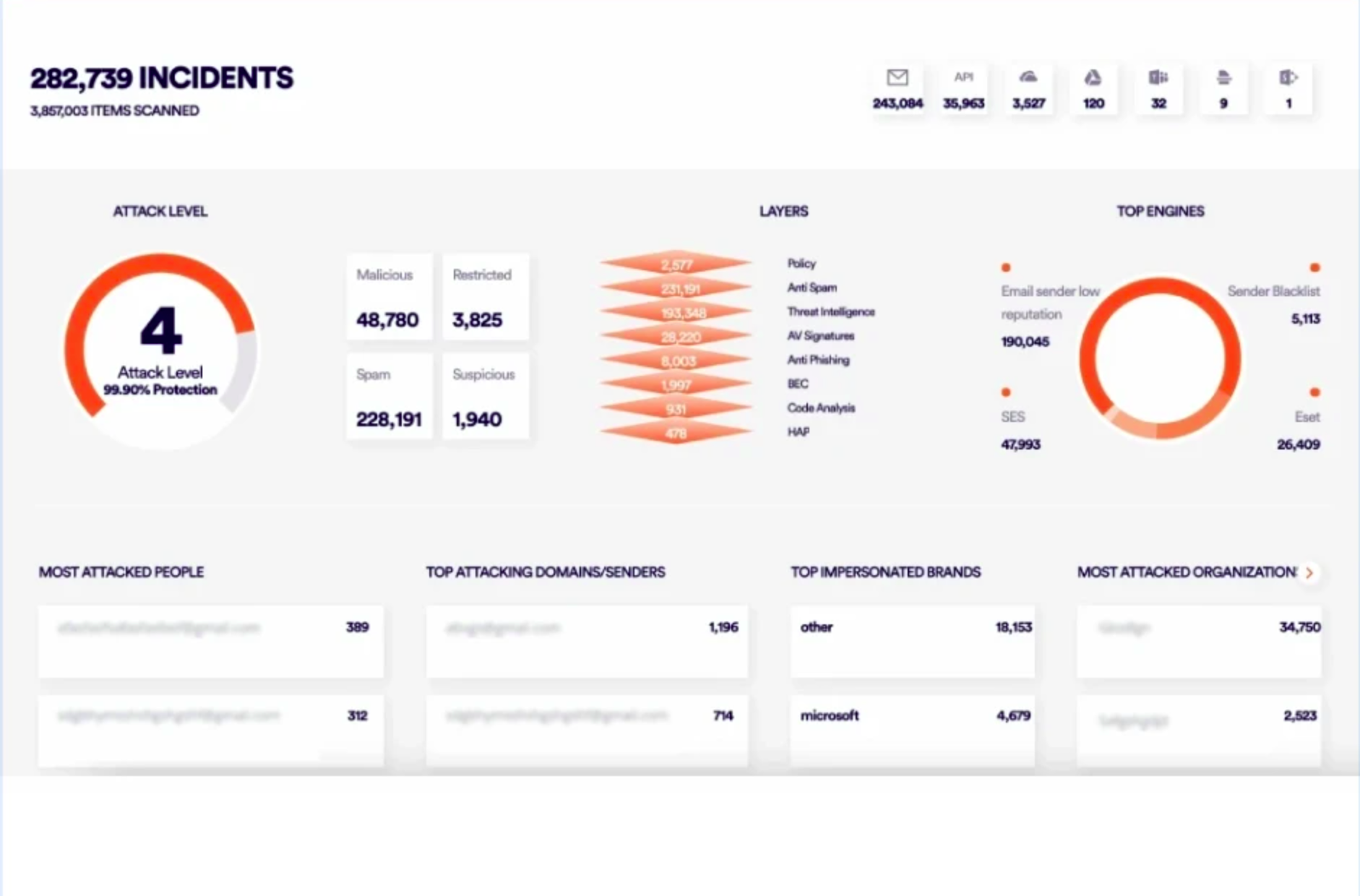
Advanced Email Security:
Intercept any email-borne threat before it reaches clients
“94% of malware is delivered via email”
Source: CSO Online
Email is still the biggest threat vector for clients. Empower them with email protection against phishing, spoofing, business email compromise (BEC), malware, zero-day attacks and advanced persistent threats (APTs). Prevent threats before they reach clients’ Microsoft 365, Google Workspace, Open-Xchange, or on-premises mailboxes.
- Anti-phishing and anti-spoofing engines
- Anti-evasion technologies
- Next-generation dynamic detection against zero-days and APTs
Stay ahead of emerging threats with smart protection plans
“Traditional antiviruses miss an average of 60% of attacks”
Source: “The Third Annual Study on the State of Endpoint Security Risk”, Ponemon Institute, 2020
Implement proactive policies against emerging threats and prevent downtime and data loss. CAL Cyber Protection Operation Centers (CPOCs) monitor the threat landscape and release actionable alerts, which can be automatically applied. This approach can result in more frequent backups, deeper anti-malware scans, specific patch installs, etc.
- Proactive protection against emerging threats
- Monitor the threat landscape
- Automatically adjust protection policies
Prevent data loss for your clients with best-in-class data protection
For clients’ business-critical data, backup is not enough. To avoid data loss, you need an integrated approach to cyber protection, ensuring backed up data is protected against today’s threats.
“60% of SMBs that go through a data loss incident go out of business within 6 months”
Source: National Cyber Security Alliance
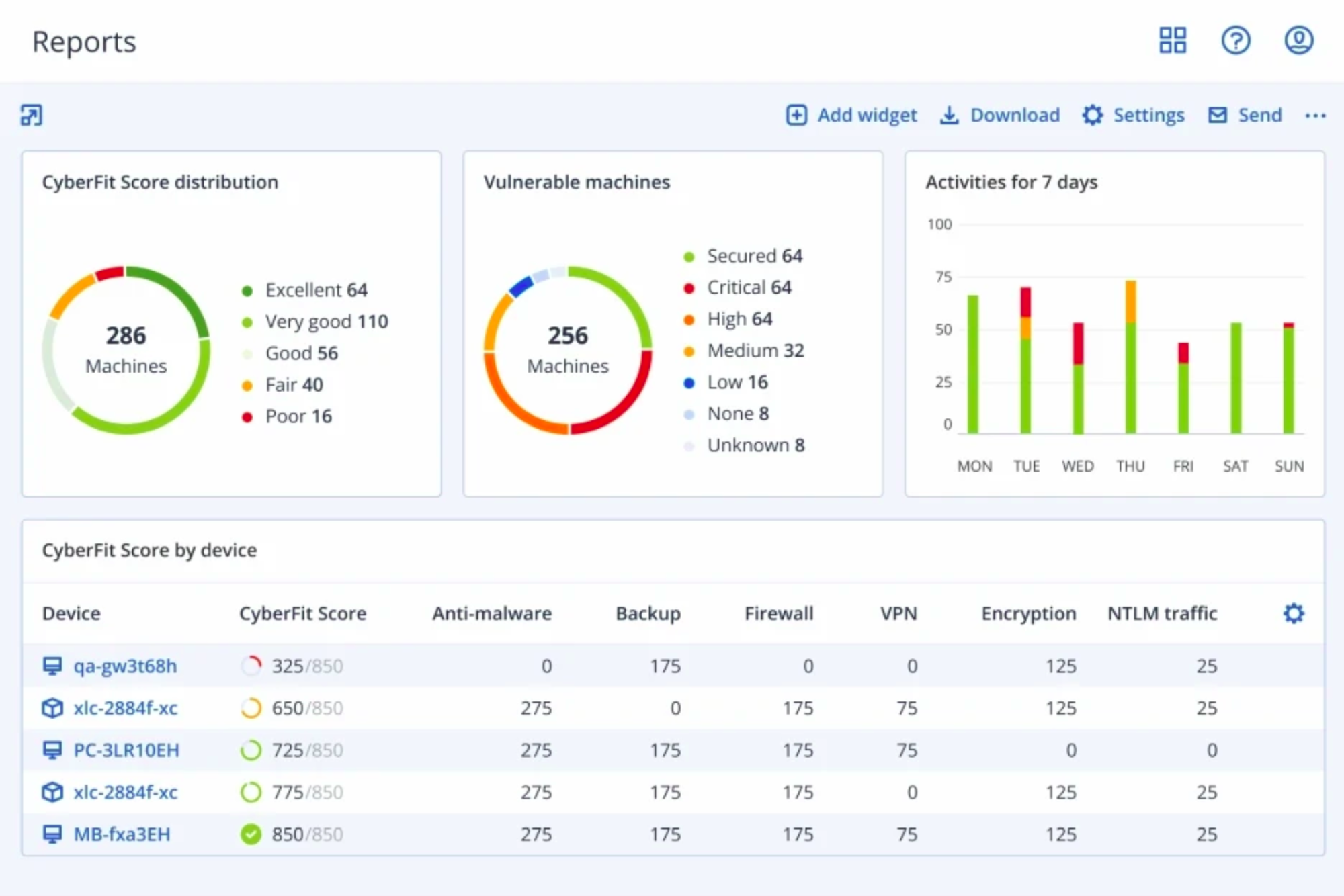
Strengthen your clients’ security posture with security assessment services
Every change to your clients’ IT environment or processes inadvertently introduces new risks and potential security gaps. CAL Security Assessment Services enable you to apply a proactive approach to review a client’s security program and enhance your services with MSSP-level services.
- Risk Assessment
- Vulnerability Scanning
- Penetration Testing
- Social Engineering
- Remediation Plan
Prevention is just one stage of modern cyber protection
To enable partners to deliver thorough protection for their clients, CAL vision and products are based on a multi-stage process rather than simply detecting and blocking threats, leaving other risks unaddressed.
Prevention
Don’t wait for threats to hit, proactively protect your clients and limit their attack surface.
Detection
Detect issues and threats in real-time before they pose risk to the IT environment.
Response
Enable quick actions that immediately mitigate the risks before damage occurs.
Recovery
Restore client data quickly and safely so no data is lost, with near-instant availability, in case of compromise.
Forensics
Mitigate future risks and enable easy investigations by collecting forensics information.
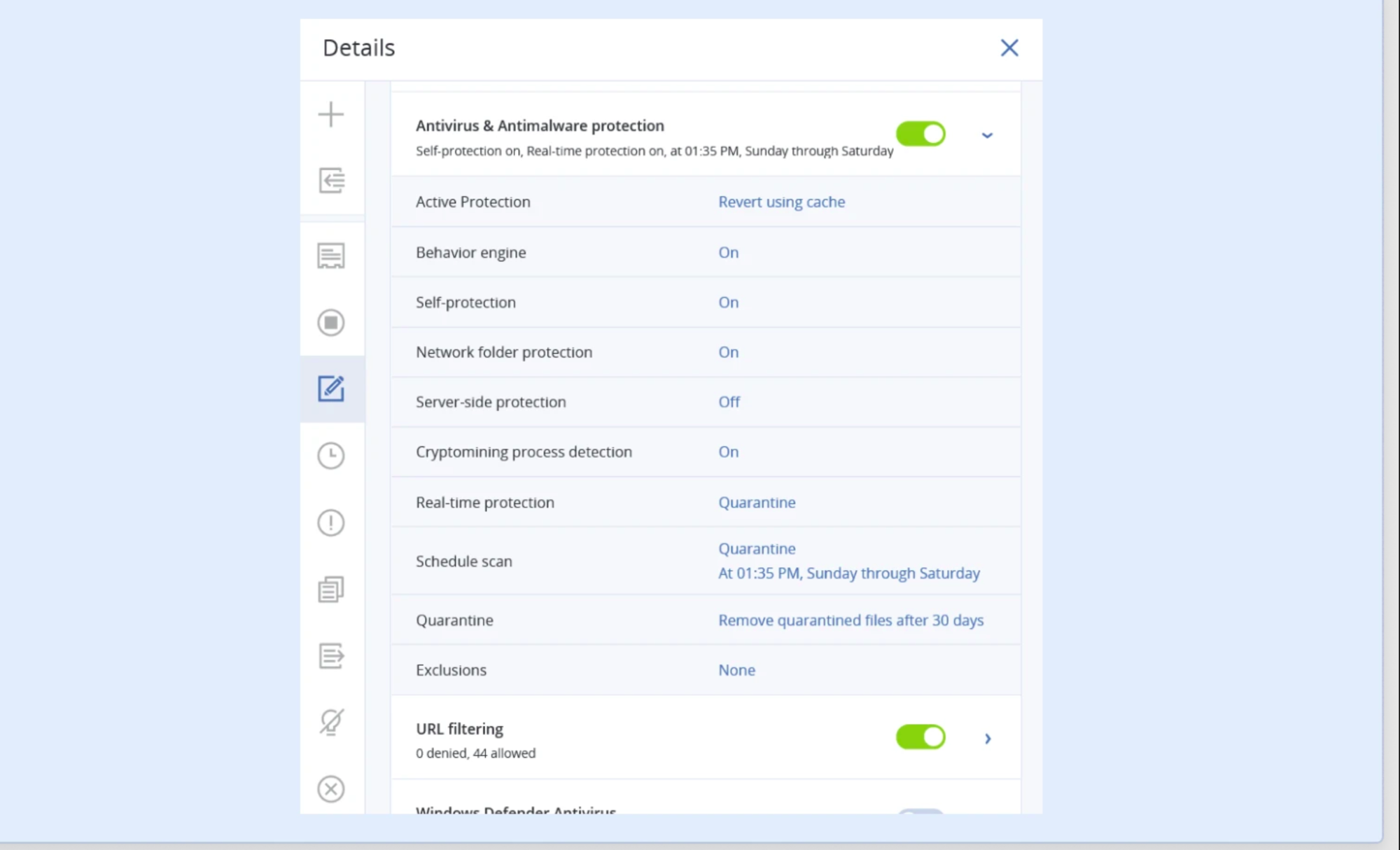
Managed Anti Malware Protection
From mom-and-pop shops to large firms, modern businesses face a flood of sophisticated new cyberthreats that threaten their very existence. Offer best-in-breed security services for your clients’ entire workloads — data, applications, and systems — built on CAL advanced, next-generation anti-malware protection solutions.
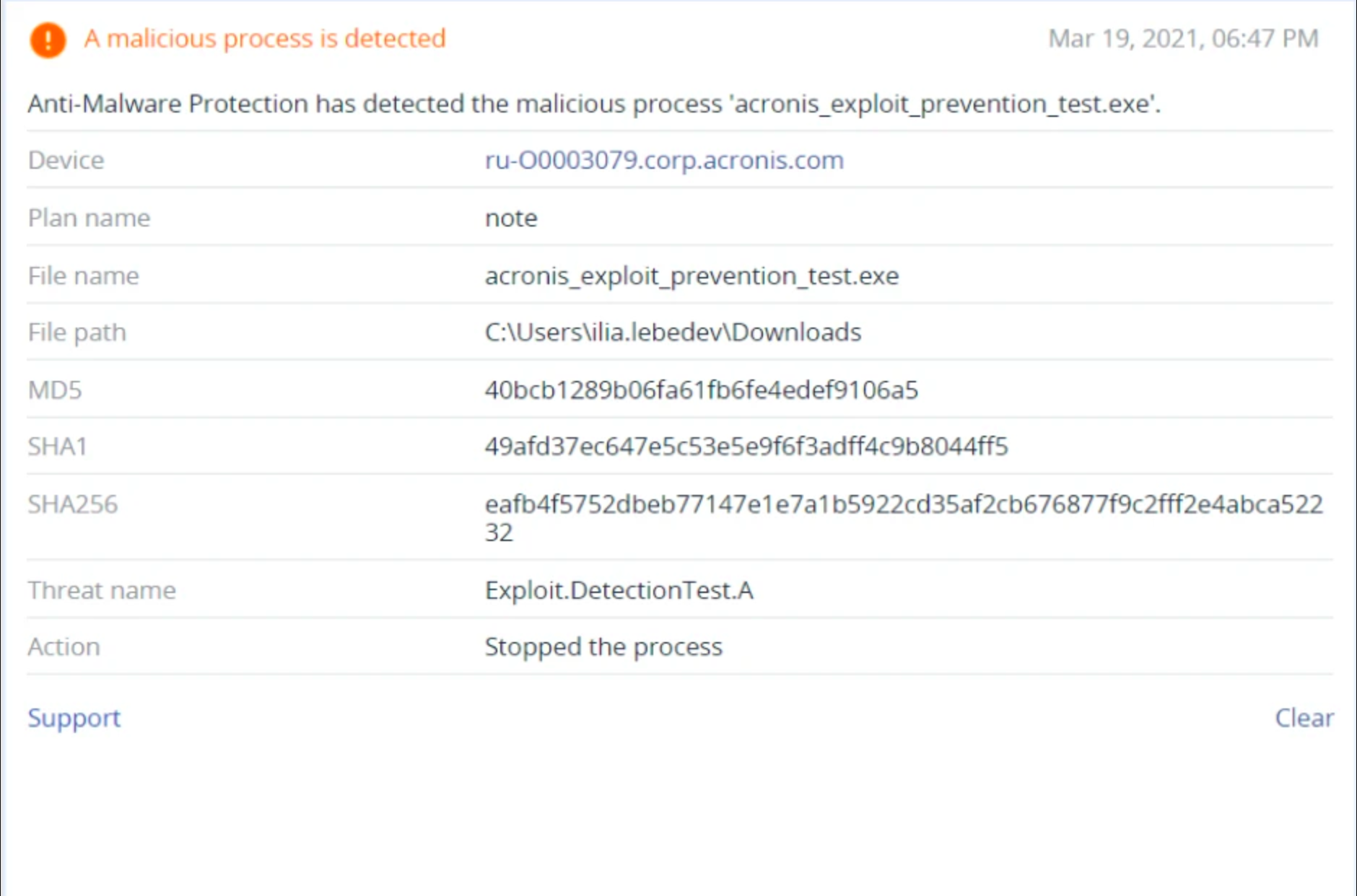
Handle any cyberthreat — even those never before seen
Malware evolves at blinding speeds. Solutions that rely solely on signature-based detection can’t come close to keeping up with the daily onslaught of new ransomware, worms, and Trojans. CAL AI-powered anti-malware engine uses advanced behavioral heuristics to detect the processes that indicate malicious activity — and immediately shuts them down before harm can come to your clients’ systems or data.
Minimize Complexity Of Management
As businesses demand more from their IT services, MSPs are adopting more and more disparate tools that don’t work together smoothly. Managing this patchwork of defenses is time-consuming, and creates protection gaps that leaves clients exposed. CAL unique integration of advanced anti-malware security with best-in-breed backup and endpoint protection management enables greater efficiency and seamless remediation — no need to juggle multiple solutions.
Ensure Complete Cyber Protection
Modern malware takes many forms. CAL solutions employ multiple layers of defense to protect your clients and their data against any threat, from malicious injections and backdoors to obfuscated malware and fileless attacks. Scan backups both as they’re created and as they’re retrieved to ensure data integrity. Even zero-day threats can be contained, thanks to advanced behavioral detection that identifies and blocks suspicious processes.
Managed Patch Management Services
Your clients rely on a variety of applications for daily operations, and each of these represents a possible avenue of attack for cybercriminals. Vulnerability fixes are released frequently, but with such a high volume of updates, manual patch management is a daunting task for service providers — and time is of the essence. CAL automated patch management solutions eliminate complexity, enabling you to keep client systems protected against the latest threats with minimal effort.
Proactively protect client systems and data
New vulnerability fixes for business-critical tools are released frequently — but until these patches are actually applied, your clients remain unprotected. CAL integrated vulnerability assessment capabilities can identify systems and applications that require updates, deliver detailed reports about the IT environment, and enable you to easily roll out patches on-demand or on a scheduled basis through an intuitive dashboard. CAL solutions support hundreds of popular third-party applications.
Ensure Continuity With fail-safe patching and cloud patch management
Patches aren’t perfect — even well-tested updates can potentially conflict with other applications or operating systems. With CAL solutions, you can automatically back up client systems before deploying a new fix. If there’s an issue post-update, it’s quick and easy to roll back systems to a known working state, ensuring smooth operations and the safety of business-critical data.
Continuous Data Protection
Data loss and downtime can be devastating to any organization. As a service provider, you need the ability to quickly restore all of your clients’ business-critical data — not just last week’s backups. CAL solutions enable you to deliver continuous data protection services, supporting integrity of data and operations.
Save Their Data, Save The Day
Delight your clients with the ability to restore business-critical files and folders, no matter when their last scheduled backup was performed. Data is at the core of modern business operations — if lost, the resulting interruptions can lead to serious financial and reputational harm. CAL continuous data protection capabilities let you deliver near-zero RPOs and downtime. Your clients will love you for it.
Protect Clients' Workload In Real Time
Differentiate your business with unparalleled data protection flexibility. CAL agent monitors and backs up every change made to critical applications and files, allowing you to choose a recovery point just seconds before the data loss event occurred. Integrated anti-malware capabilities ensure the integrity of backed-up data and enable seamless remediation.
Solution For Hosting Service Providers
More than cyber protection and backup – CAL enables Cloud and Hosting Service Providers to deliver modern, comprehensive cyber protection solutions that are profitable and ready to deploy.
The Internet Faces New Risk
Drives, data, and networks are still real risks. But Cloud & Hosting environments now face increasing threats from malware, ransomware, and more. Legacy backup and security solutions are inadequate to defend against modern threats.
Cloud & Hosting Have Changed
CAL delivers complete cyber protection that is ready to deploy on any infrastructure with the control panels and automation tools you use now. It’s cloud optimized and built to scale, enabling you to protect your servers, create profitable bundles that drive MRR, and reduce churn with the convenience of an all-in-one solution.
Complete, Modern Cyber Protection
Protect your entire infrastructure from cyberthreats and data loss and achieve data sovereignty objectives using a single pane of glass on a platform designed by hosters for hosting.
Enable Premium Bundles With Higher MRR
Build upon CAL Defense to create bundles and add-ons that enable customers to access premium protection for their data, applications, websites, and systems.
Extend Cyber Protection Services to Cover Additional Customer Workloads
Extend your cyber protection solutions out to customer environments – protecting data, applications, and systems of their teams.
Deploy Seamlessly Using The Tools You Have Now
CAL Defense is ideal for Hosting and Cloud with deep integrations into the control panels and automation systems you use today.
How to purchase ? Please contact us via chat or the contact form
Socials

Aerospace & Defense Company
Important
Our Industry
Government
National Security
Aerospace
Defense
Healthcare
Information Technology
Financial Services
Maritime
© Copyright 2022 . All Rights Reserved. Cyber Aeronautycs Ltd .
Registered in Bangladesh . Company Registration Number C-172611