CAL Defense - Lifetime deal is out . Click Here
Welcome To Cyber Aeronautycs Ltd.
SECURING AIR & GROUND INFRASTRUCTURE
We are an aerospace and defense company in Bangladesh and engaged in research, design , development, manufacture, integration and sustainment of advanced technology systems, products and services.
Protect all clients, whatever their hardware, software, or use case
Overcoming the growing complexity of IT infrastructures and sophisticated cyber attacks requires a comprehensive backup solution to keep every bit of data safe.
State-of-the-art management
Work efficiently, effectively and worry-free – you can protect all clients from a central, multi-tenant, web-based portal
Protection for 20+ platforms
Boost productivity working with just one solution for any customer workload – physical, virtual, cloud, or mobile
The most secure backup
Guarantee client security with data protection that’s secured with AI-based anti ransomware, file notarization, and end-to-end encryption
File and disk-image backup
Backup individual files or safeguard your entire business by backing up the entire system as a single file, ensuring a bare metal restore capability. In the event of data disaster, you can easily restore all information to new hardware.
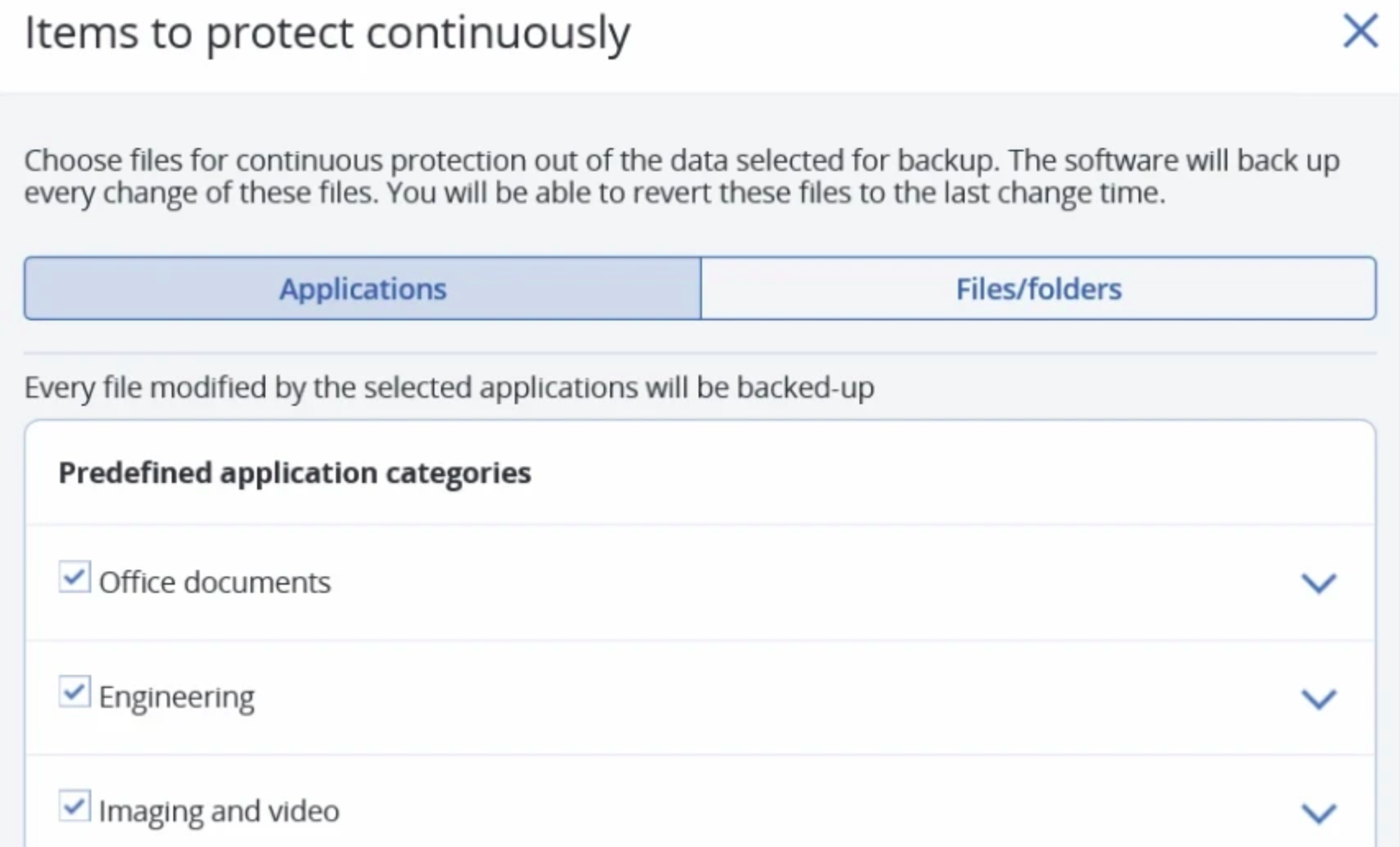
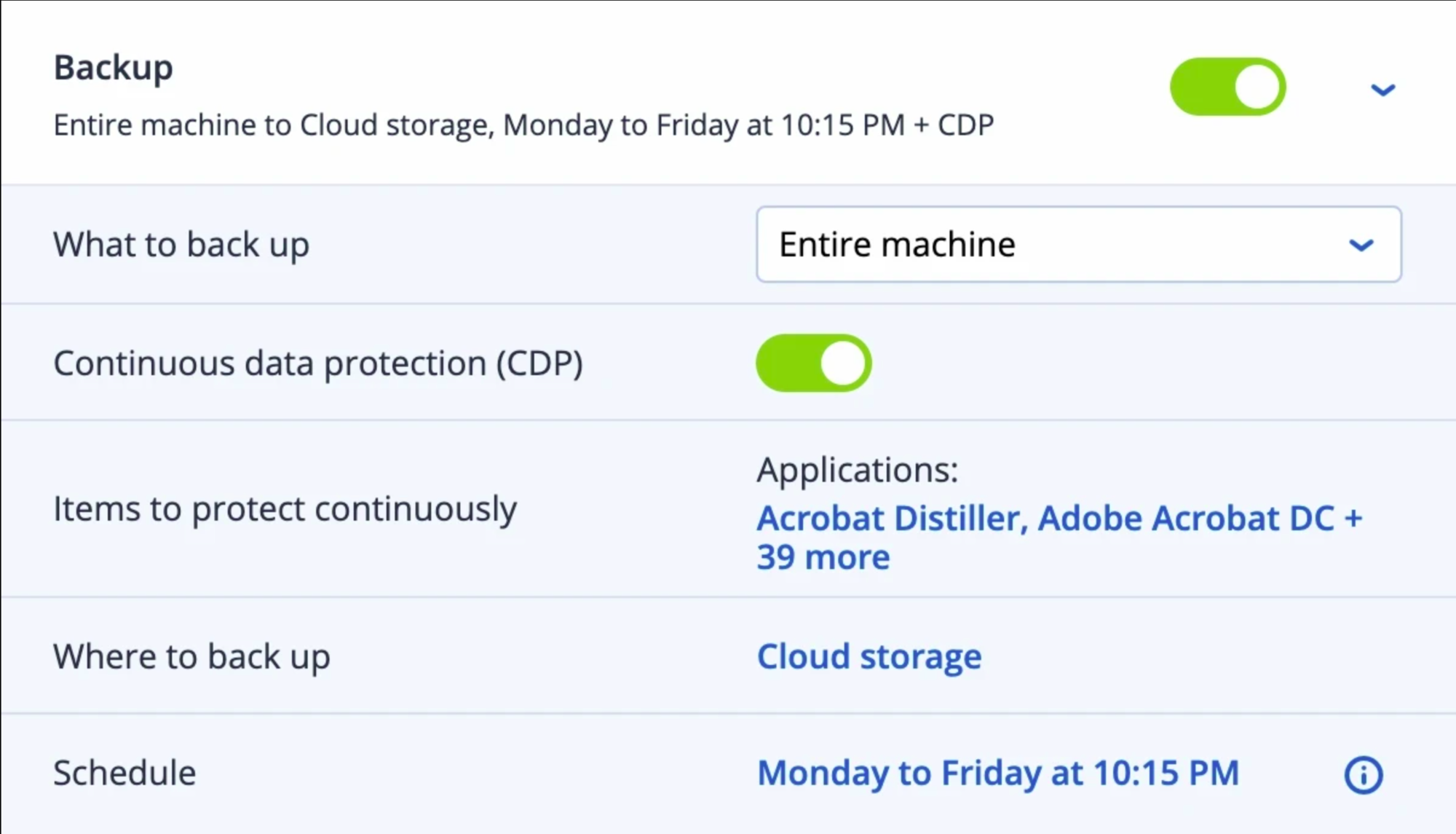
Continuous data protection
Ensure users don’t lose their in-progress work by defining a list of critical apps that are frequently used. CAL’ agent monitors every change made in the listed applications—no matter where the user saves the file – and continuously backs it up. If the system needs to be reimaged, you can restore the data from a backup and apply the latest changes, so no data is lost.
Microsoft 365 and G Suite protection
Increase revenues easily by delivering efficient, in-demand, cloud-to-cloud backup and recovery for Office 365

Profit From The Rising Demand
EMC reports 80% of businesses using SaaS have lost data. Earn more monthly recurring revenue by providing the protection services your clients need for their cloud-based applications.

Deliver Complete Protection
Protect Microsoft Exchange Online, Microsoft Teams, Sharepoint Online, OneDrive for Business, Gmail, Drive, etc. with flexible recovery options and backup search capabilities.

Avoid upfront costs while simplifying the configuration process and regular maintenance. It’s easy because there's no need to install any software.
We serve a wide range of companies
Overcoming the growing complexity of IT infrastructures and sophisticated cyberattacks requires a comprehensive backup solution to keep every bit of data safe.
CAL Defense integrates backup with advanced anti-ransomware technologies to keep your data safe from any threat.
Flexible storage
Balance the value of data, infrastructure and any regulatory requirements with flexible storage options. Grow with ease using the storage that fits your needs: NAS, SAN, tapes, disks, CAL Cloud or any private or public cloud, such as Azure, AWS or Google.
Any-to-any migration
CAL stores data in a unified backup format so that you can easily recover to any platform, regardless of the source system. Reduce risk and IT overload by migrating between different hypervisors and to/from physical machines (P2V, V2V, V2P and P2P) or the cloud (P2C, V2C, C2C, C2V and C2P).
CAL Universal Restore
Minimize expensive downtime by restoring Windows and Linux systems to dissimilar hardware, including bare-metal physical, virtual or cloud environments. By overcoming compatibility issues, CAL Universal Restore technology ensures quick and easy system migration with a few clicks.
CAL Instant Restore
Reduce recovery times with best-in-industry RTOs by immediately starting your backup as a Windows or Linux virtual machine directly from storage. Have your VM up and running in mere seconds, while CAL Instant Restore technology invisibly moves your data to the host in the background.
Variable block-size deduplication
Protect more systems while reducing the impact on disk-storage and network capacity by capturing only the blocks with data that has changed since the previous backup. CAL Backup deduplication minimizes storage space by detecting data repetition and storing the identical data only once.
Drive health monitoring
Avoid unpredictable data loss and proactively improve uptime by monitoring drive health. By using machine learning on S.M.A.R.T. reports, and various operating system parameters, CAL Defense can alert you about a disk issue before it happens. This enables you to take the precautionary measures needed to protect your data.
Anti-malware scanning of backups
Prevent restoring infected files from backups with built-in malware scanning. By scanning full disk backups at a centralized location, CAL Defense can help find malware – ensuring users restore a clean, malware-free backup.
Safe Recovery
An OS image or application in a backup that is infected with malware can cause continuous reinfection if it is used for recovery without removing the malware. Removing the detected malware and applying the latest anti-malware definitions during the recovery allows users to restore the OS image safely, reducing the chance of reinfection.
Data Protection Map
Ensure that critical data is protected for compliance reporting with a data protection map. Get detailed information about stored data and use the automatic data classification to track the protection status of important files. You will be alerted if files are backed up or not, helping you to further protect your data.
App allowlisting based on backups contents
Ensure that critical data is protected for compliance reporting with a data protection map. Get detailed information about stored data and use the automatic data classification to track the protection status of important files. You will be alerted if files are backed up or not, helping you to further protect your data.
Forensic data collection
Maintaining compliance and running internal investigations can be an expensive process. With the Forensic Mode built into CAL Defense, you can simplify future analysis by collecting digital evidence – like memory dumps and process information – from disk-level backups.
Tape Multiplexing
Maximize the effective use of tape drives during backup and recovery by allowing multiple clients to back up to a single tape drive simultaneously. Use this method when a tape drive is faster than the backup source, as it allows the tape drive to keep spinning, avoiding writing interruptions.
Tape Multistreaming
Utilize all available tape devices on your system by allowing the backup of a single client to run simultaneously to multiple tape drives. Use this method when you have multiple destination devices and would like a single backup job to utilize them all simultaneously at the time of backup.
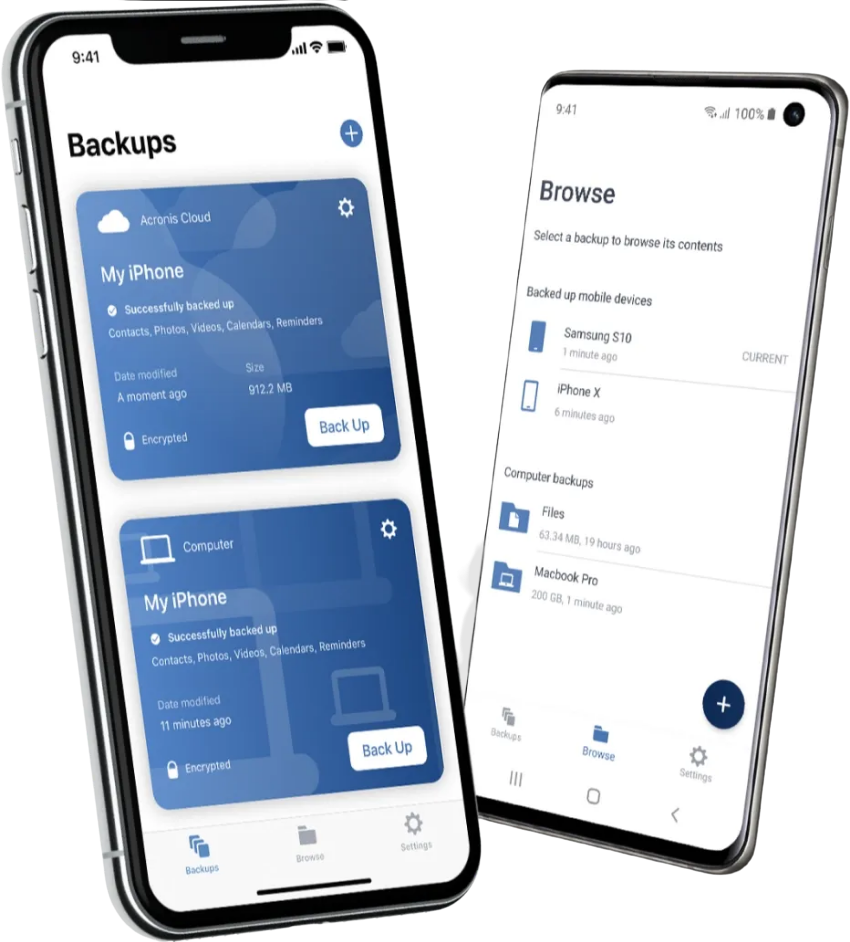
Mobile Backup
Keep your mobile contacts, calendars, photos and files safe. Our free Acronis Mobile app safeguards your device, as well as all of your family’s smartphones and tablets with CAL Defense Home Office.
Frequently asked questions about startups
You first need to create a customer and an account for them. Once that is done, you can either log in as that customer or, in the Account management console, select the customer to manage their backups. This will bring you to the Backup management console where you can download the backup agent.
1. Resource usage is relative to the system specifications and a number of other factors, such as disk speed, disk size, available bandwidth, etc. By default, the CAL backup process runs on low priority, with the operating system dynamically throttling its resources.
2. On modern servers and workstations, the CPU usage is typically around 3-4% and RAM consumption will be up to 500 MB with CPU spikes during the snapshot phase.
We provide a hardware-independent software solution that can work with almost any hardware on industry-standard protocols like SMB and NFS. We can also support any block-based storage, as long as it's supported by the operating system.
This will depend on the size and performance of the hard disk, the amount of data changed, and the available bandwidth. Testing needs to be done, but the minimum threshold is 10 minutes.
Compression rates vary depending on the type of data but generally, you can expect around 30-40% compression unless the data is exclusively media files.
Yes, physical-to-virtual migration is available in CAL Defense. This operation can be performed if at least one Agent for VMware or Agent for Hyper-V is installed and registered.
- For a backup to Cloud, an active CAL Cloud Storage subscription is required.
- Create a new backup plan and choose "Cloud Storage" as a destination in the field "Where to back up".
How to purchase ? Please contact us via chat or the contact form
Socials

Aerospace & Defense Company
Important
Our Industry
Government
National Security
Aerospace
Defense
Healthcare
Information Technology
Financial Services
Maritime
© Copyright 2022 . All Rights Reserved. Cyber Aeronautycs Ltd .
Registered in Bangladesh . Company Registration Number C-172611
